The most complete JWT check coverage of any Burp extension. Every known JWT attack vector, misconfiguration, and CVE.
A01Algorithm None attack — all 16 case permutations of "none"High
A02Invalid signature accepted — verification not enforcedHigh
A03Signature stripping — empty signature acceptedHigh
A04Expired JWT accepted by serverHigh
A05Empty secret key accepted (HMAC with empty password)High
A06Weak secret brute force — 200+ built-in + extracted secretsHigh
A07Algorithm confusion RS256→HS256 with real JWKS public keyHigh
A08JWK header injection — self-signed key embedded in tokenHigh
A09JKU header injection — attacker-controlled JWKS URLHigh
A10JKU SSRF pingback — server makes outbound requestMedium
A11X5U header injection — attacker-controlled certificate URLHigh
A12X5C header injection — self-signed certificate in tokenHigh
A13KID path traversal — 10+ traversal paths including /dev/nullHigh
A14KID SQL injection — UNION SELECT, OR bypass, error-basedHigh
A15KID command injection — time-based with sleep payloadsHigh
A16KID LDAP injection — wildcard and filter manipulationHigh
A17Not Before (nbf) claim not enforcedMedium
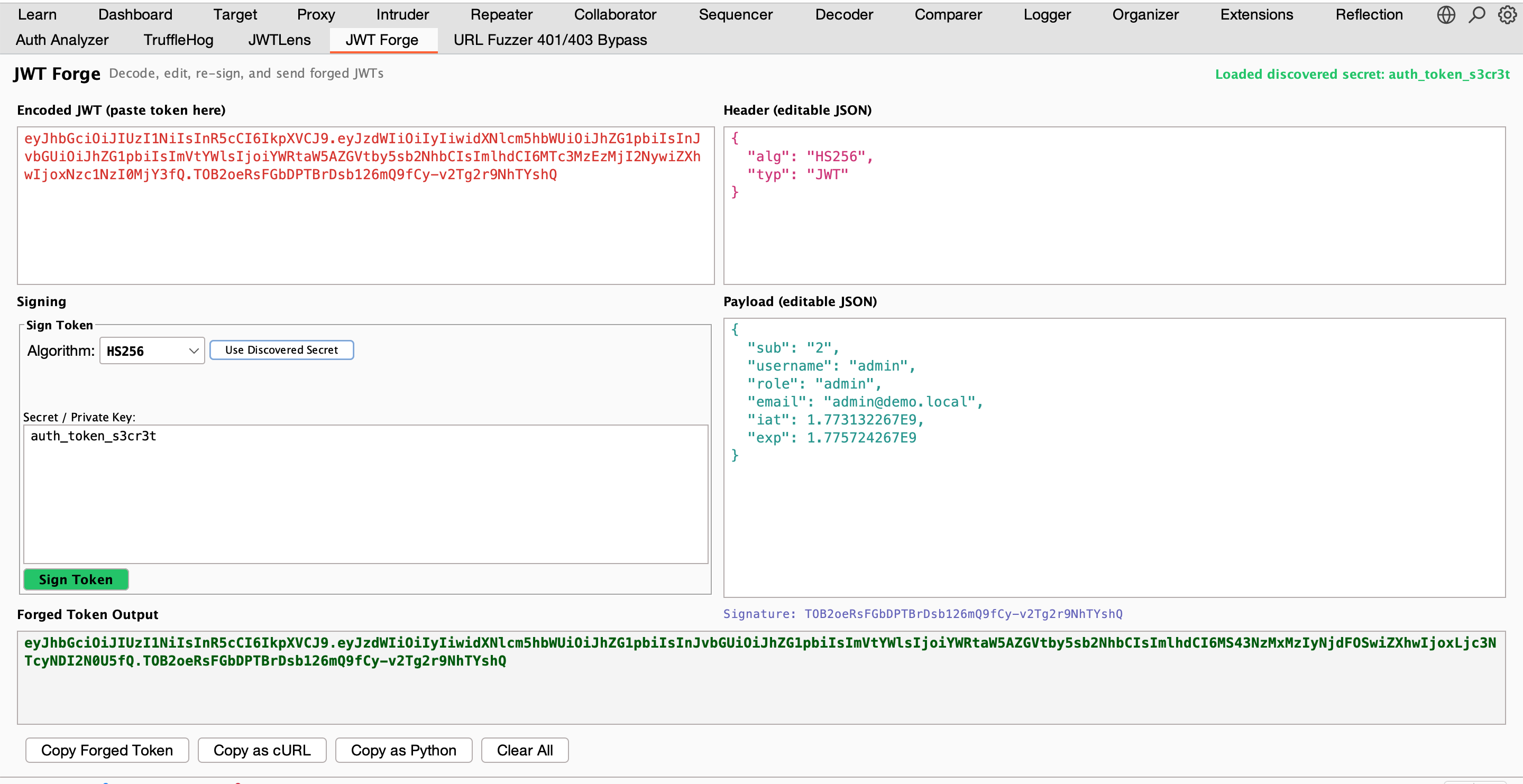
A18Claim tampering — admin, role, sub privilege escalationHigh
A19Subject claim enumeration — user ID discoveryMedium
A20CVE-2022-21449 Psychic Signatures — Java ECDSA zero bypassHigh
A21ECDSA signature malleabilityLow
A22Cross algorithm signing — HS384, HS512 with empty/known keyHigh
A23Null signature bytes acceptedHigh
A24Token accepted beyond reasonable clock skew toleranceMedium
A25Algorithm confusion with forged public key (Sign2n)High
A26Weak RSA key size — modulus under 2048 bitsHigh
A27JWKS endpoint discovery — well-known pathsInfo
A28Payload modification accepted without re-signingHigh
A29typ header manipulation acceptedLow
A30Token confusion between endpoints — cross-service replayMedium
A31Token still valid after logoutMedium
A32Token still valid after password changeMedium
A33JWKS spoofing via well-known path overrideHigh
P01JWT detected in HTTP trafficInfo
P02JWT exposed in URL query parameterMedium
P03JWT exposed in URL fragmentMedium
P04JWT cookie missing HttpOnly flagMedium
P05JWT cookie missing Secure flagMedium
P06JWT cookie missing SameSite attributeLow
P07JWT missing expiration (exp) claimHigh
P08JWT has excessive lifetime (configurable threshold)Low
P09Sensitive data in JWT payload — emails, passwords, API keysMedium
P10Expired JWT still being sent in requestsInfo
P11Missing issuer (iss) claimLow
P12Missing audience (aud) claimLow
P13Symmetric algorithm detected — brute force advisoryInfo
P14JWT leaked in HTTP response bodyMedium
P15kid (Key ID) parameter presentInfo
P16jku (JWKS URL) parameter presentLow
P17x5u (X.509 Certificate URL) parameter presentLow
P18x5c (X.509 Certificate Chain) parameter presentLow
P19jwk (Embedded JSON Web Key) parameter presentLow
P20Nested JWT detected inside payloadInfo
P21Weak or deprecated signing algorithmMedium
P22Missing not before (nbf) claimInfo
P23Missing unique identifier (jti) claimInfo
S01JWT signing secret extracted from JS/JSON/HTML responseHigh
S02RSA/EC private key exposed in HTTP responseHigh
S03RSA public key found in HTTP responseLow
S04Inline JWKS found in response bodyLow
S05JWKS URL reference discovered in responseInfo
S06Base64-encoded secret decoded from responseHigh